The Endowment Effect
People overvalue what they believe they already own. How skilled operators manufacture premature ownership to make walking away feel like losing something real.
Read Article
The Complicity Gradient: How Manipulators Turn Bystanders Into Accomplices
Nobody wakes up one morning as an accomplice. The complicity gradient converts targets into participants through a sequence of trivial compromises, each one too small to refuse and too connected to the last to undo.
Read Article
The Kafkatrap: When Your Denial Becomes Their Evidence
The closed loop of accusation where every response confirms guilt. From Salem's spectral evidence to McCarthy's loyalty hearings, the pattern that makes innocence logically impossible.
Read Article
The Competence Trap: How Your Excellence Becomes Your Cage
Controllers do not punish excellence. They reward it just enough to prevent escape. Your talent becomes the instrument that locks you in place.
Read Article
The Unfinished Loop: How Incomplete Tasks Become Instruments of Control
Your brain treats an unfinished conversation like an open wound. Manipulators know this. They leave things deliberately incomplete, because the gap itself is the leash.
Read Article
The Clock Reset
Trump set a 48-hour ultimatum to Iran on Friday. On Monday he extended it by five days. This is not a reversal. It is a precision leverage instrument. The deadline is not a clock. It is a room.
Read Article
The Mimetic Trigger: How Desire Gets Engineered Through Imitation
You do not choose what you want. Someone places the right model in front of you and lets your nervous system do the rest. From Bernays's 1929 parade to modern platform architecture.
Read Article
The Identifiable Victim Effect
A single named face commands more generosity than a million statistics. How this cognitive mechanism operates, how it gets weaponized, and how to recognize it before your emotions are spent.

The Parasocial Bond
Manufactured intimacy at scale. How figures engineer one-sided relationships that feel personal, extract loyalty, and bypass critical evaluation entirely.
Read Article
The Strategic Vulnerability
Calculated self-disclosure of weakness to manufacture trust, disarm opposition, and extract reciprocal leverage. The person who confesses first rarely loses.
Read Article
The Exit Frame
Before a conflict ends on the ground, it must end in the public mind. How White House advisers are constructing the psychological architecture of withdrawal from the Iran war.
Read Article
The Agenda-Setting Effect
The most durable influence operation controls what you think about, not what you conclude. How salience engineering works and why it is more powerful than persuasion.
Read Article
Motivated Reasoning
You think you are reasoning toward a conclusion. You are almost certainly reasoning away from one. How the mind hijacks logic to protect desire, and what to do about it.
Read Article
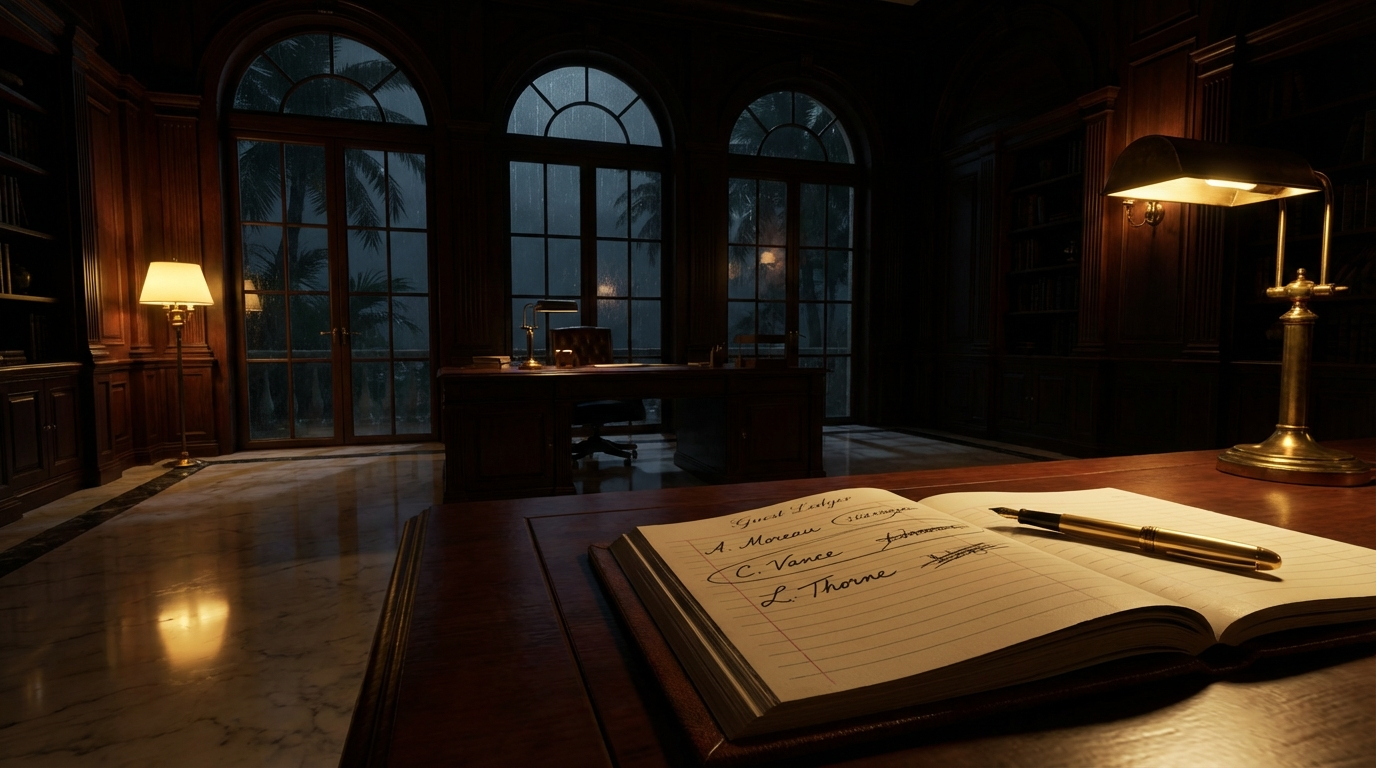
The Honeypot Extraction
How O'Keefe's "Dating the Deep State" used manufactured romantic intimacy to lower psychological defenses, extract private political statements, and convert them into federal termination weapons.
Read Article

Terror Management Theory
How mortality awareness drives luxury consumption, political tribalism, and legacy-building. The mechanism behind every significant human decision you believe you are making rationally.
Read Article
The Semmelweis Reflex
Why institutions reject evidence that threatens established doctrine. The psychology of automatic dismissal, how it operates, and how to breach it.
Read Article
The Loyalty Test
When DOGE operatives told a cooperative official they'd "prefer" he remain on their side, they weren't expressing a preference. A dissection of the structured threat that converts compliance into perceived consent.
Read Article
The Tactical Apology
Not every apology is remorse. Some are precision instruments designed to end scrutiny and restore access without cost. Four forms, two real-world case studies, and the three diagnostic tests that distinguish repair from manipulation.
Read Article
The Manufactured Dependence
How power players systematically dismantle self-sufficiency and engineer conditions where targets cannot function without them. From the British East India Company's deindustrialization of Bengal to the petrodollar architecture to interpersonal isolation.
Read Article
The Zone Flood
Russia suspended 800 million X accounts in 2024. The goal was not persuasion. It was saturation. How flooding a platform with coordinated fake accounts hijacks social proof and collapses critical thinking by volume.